
In-House Platform vs Managed System of Engagement: When to Outsource Messaging
When deciding between in-house platforms and managed systems for messaging, prioritize operational risk and outcomes over code ownership. A managed system can enhance control by ensuring reliable writebacks and compliance, allowing you to focus on what truly matters.
Owning the stack feels like control. In regulated operations–and especially when it comes to communication workflow automation–it often isn’t. Deciding when to outsource messaging is the real decision in front of most ops leaders. Control means evidence you can defend, reliable writebacks, and predictable cycle time. A managed system can give you more of that, not less, because it takes on the work that fails most often and backs it with guarantees.
In this article we’ll walk you through a practical lens. If you must wire legacy cores and modern APIs, verify identity across channels, encode policy, and prove outcomes to audit, you’re not choosing between tools. You’re choosing who carries the operational risk when things go wrong. The mistake is equating “we built it” with “we can control it.” Control shows up as posted payments, plans created, flags cleared, and logs you can hand to compliance without a scramble.
Key Takeaways:
Treat “control” as evidence, writeback success, and SLA-backed reliability, not code ownership
Quantify DIY risk across integration, identity, policy, and audit before you pick a path
Use a readiness checklist to test bandwidth, incident posture, and compliance depth
Measure vendors on writeback guarantees, telemetry depth, and audit trails, not demos
Start with one high-volume workflow to prove resolution, deflection, and cost reduction
Shift reporting from conversations to outcomes: completion, time-to-resolution, writeback success
Why In-House Platforms Feel Safe But Shrink Real Control
In-house feels safer because you can see the code, set the backlog, and staff the fixes. Real control in financial services is different, it is writebacks that land, identity you can trust, and audits you can pass. When those break, you lose time and credibility. A managed system can raise control by owning the riskiest steps and proving outcomes.
What “Control” Means In Regulated Operations
Control is not meetings and roadmaps. Control is the ability to show that a payment posted, a plan was established, a document was captured, and consent was time-stamped. You need idempotent transactions so retries do not double-charge. You need traceable identity checks so a regulator can follow the path. Without that, decisions don’t stick.
I’ve watched teams spend months building flows that look polished while the hard parts remain manual. The cost isn’t just delay. It’s operational debt that pops up during incidents and audits. You feel in charge until a backlog of mismatched records forces manual reconciliation at scale. That’s when “we own it” starts to feel like “we can’t prove it.”
Where Control Breaks: Writebacks And Evidence
Most failures hide at the last mile. A card update form that doesn’t validate properly. A payment that “succeeds” in the UI but never posts to the ledger. A plan that looks set in a CRM but never hits the collections engine. The logs are thin, and the audit trail is missing the key field you need.
Those gaps create a double cost. Your team reworks the case, and customers call because their balance didn’t change. Each case looks small, but at volume the waste is real. You also invite risk. Identity steps that aren’t aligned to guidance like the NIST SP 800-63-3 digital identity guidelines can fail a review. Control is the proof you can hand over, not the comfort of owning code.
Outsourcing That Increases Control
Outsourcing raises control when it moves the riskiest steps under contract. You get service levels for retries and backoff, identity steps that match policy, and writebacks that don’t duplicate under load. You also get telemetry you can trust, not a patchwork of system logs stitched after the fact.
The key is picking a partner who encodes policy, handles exceptions, and proves outcomes. If they only send messages, you’ll still reconcile by hand. If they don’t own integration, you’ll still wait on engineers. If they can’t show you evidence, you’ll still scramble at audit time. Real outsourcing reduces risk you can count.
Reframing Control Around Outcomes And Evidence
Control improves when you centralize the outcomes, not the tools. If the message is where action starts, finish the task there and write back to the system of record. That removes channel switches that cause abandonment and creates a single place to prove what happened. When outcomes sync automatically, you measure completion, time-to-resolution, and deflection, not just sends.
The Real Bottleneck Is Integration, Not Chat Flows
Most stacks can draw flows fast. The struggle is safe, reliable transactions with legacy cores and modern APIs. Identity checks across channels, schema mapping, retry logic, and idempotency are where projects stall. If any of those steps is weak, completion drops and risk rises.
I’ve seen teams underestimate error handling more than anything else. Retries without jitter can flood a downstream system. Missing idempotency keys can double-charge under network flaps. These aren’t edge cases, they are daily realities in distributed systems. Guidance like AWS’s backoff with jitter exists for a reason.
Evidence, Audit, And Idempotency Define Outcomes
Evidence turns work into decisions you can defend. You need event logs that show who acted, when they acted, what they saw, and what posted. You also need idempotent writebacks so a retry doesn’t create duplicates. That’s a contract between systems, not a UX tweak.
Vendors will show delightful flows. Ask for the evidence model and the retry plan. Ask how they prevent double-posting and how they reconcile partial failures. If they cannot answer plainly, control will be fragile in the moments that matter.
Counting Costs In Build vs Buy Messaging Decisions
The right choice comes from numbers, not taste. Tally the engineering months for adapters, authentication, schema mapping, retries, and monitoring. Add the ongoing incident load and the on-call you’ll need for brittle edges. Then compare it to a service that contracts for writebacks, identity, and telemetry. Many teams find DIY costs more and risks more.
Integration Project Load You Can Measure
A typical build must handle one-time setup and continuous change. New endpoints, shifting schemas, and policy updates never stop. You also have to backfill telemetry so ops can see completion, not just deliveries. Those lines on a plan hide sustained work you’ll carry every quarter.
Budgeting gets tricky when you only count first builds. The maintenance tail is where costs pile up. Think about policy changes that add an eligibility check. Think about a new channel like WhatsApp and the time to handle consent correctly. The numbers add up, then add again next year.
Operational Risk People Underestimate
Incidents don’t respect roadmaps. A transient outage hits during a peak day. A new retry path overwhelms a downstream service. A missing idempotency key recreates a payment. Teams scramble, then manually reconcile for weeks. You lose trust, not just time. Readers in ops have lived this.
Controls exist to reduce those risks, but they are easy to get wrong. Idempotency must be end-to-end, not just at the edge. Stripe’s guidance on idempotency keys shows how to guard payments, yet many internal systems still rely on timestamps or weak deduping. That is a mistake you can avoid.
Financial Impact Of Manual Reconciliation
Manual wrap-up creates a slow leak. Agents fix records case by case. Leaders miss their goals because totals don’t match. Customers call again because they still see the wrong numbers. The cost isn’t just labor. It is lost confidence and delay in cash flow.
You can cut that cost by finishing tasks in the message and writing back automatically. Then measure what matters. Completion rate. Time-to-resolution. Writeback success. Those three tell you if the leak is closed.
Life Inside A Broken Last Mile
The day feels busy, but outcomes stall. Messages go out, customers click, then bounce to a login they forgot. A handful try again. Most give up. Agents inherit half-complete journeys with no context, and the queue shifts, not shrinks. People feel it as constant churn, not progress.
Late-Night Rewrites And Angry Callbacks
You push a fix at 8 pm and wake to three new issues by 8 am. A config change “worked” in staging but failed against a quirky production API. The logs don’t show enough detail to prove what happened, so your team hunts across systems. Customers call because balances didn’t update. Trust erodes fast.
Leaders know the pressure. A regulator asks for evidence, and you have to reconstruct the path from email platform logs, CRM notes, and a database extract. The stress isn’t the volume, it’s the uncertainty. When outcomes aren’t certain, every escalation hurts.
Agents Stuck On Policy-Bound Work
Agents are great at judgment. They aren’t great at rekeying. When routine work lands with them, cycles stretch and morale dips. You pay trained people to push buttons that policy could have encoded. Everyone loses time. Customers wait, teams struggle, and your cost-to-serve climbs.
Moving routine, policy-bound work into self-service removes that burden. You also protect quality because rules don’t drift. People then focus on exceptions that truly need a human.
A Practical Way to Decide When to Outsource Messaging
Use a simple model. If a workflow touches identity, policy eligibility, and core writebacks, default to outsourcing unless you have proven, staffed capabilities in all three. Run a readiness check, quantify your risk delta, and evaluate vendors on evidence, not presentations. Then start with one high-volume workflow and measure outcomes you can trust.
Run A Readiness Check Before You Build
Start by asking five plain questions. Do you have engineers available for adapters and authentication with legacy cores and modern APIs. Do you have a clear plan for idempotency, retries, and backoff across services. Do you maintain audit-grade evidence models. Do you have channel consent and timing expertise. Do you have incident and on-call cover for messaging spikes.
Teams often realize they can handle two parts, but not all. That gap is where projects slow or fail. Write the answers down. If any are a soft “maybe,” treat it as a risk. The checklist is not gatekeeping. It is insurance against hidden cost.
After you’ve answered honestly, focus the next steps:
Map your highest-volume, policy-bound workflows
Identify which steps need human judgment and which don’t
Document systems of record for outcomes and required fields
Specify identity requirements by channel and risk class
Define evidence you must retain for audit and for how long
Quantify Risk Delta With A Simple Model
Put numbers to it. Estimate engineering months for integration and the maintenance tail. Add expected incident hours and manual reconciliation time. Then model an outsourced path with service levels for writebacks, evidence, and retries. The delta shows where you save time, reduce risk, or both.
Be conservative. If you undercount incidents, your model lies. If you ignore identity and audit, your model hides real exposure. A clear model builds confidence for leadership. It also makes tradeoffs visible. You are choosing the surface area you will carry.
Translate the math into a working view:
Cost buckets: build, maintain, incident, reconcile
Risk buckets: identity failure, writeback duplication, audit gaps
Outcome metrics: completion rate, time-to-resolution, deflection
Decision rule: outsource when risk-adjusted cost beats DIY
Vet Vendors On Evidence, Not Demos
Ask for proof. How do they guarantee idempotent writebacks. How do they handle retries with jitter under load. How do they validate identity across SMS, email, and WhatsApp. What does the audit trail capture, and how do you export it to your SIEM or data lake. Which outcomes write back, and to which fields.
You’re not being difficult. You’re protecting your customers and your team. A good partner will welcome these questions and show real artifacts. If you only see slides, you’ll inherit the risk later. If you see logs, schemas, and SLAs now, you’ll sleep better later.
Stop losing hours to manual reconciliation and start closing the loop inside the message with a managed approach. Get in touch to find out more about how RadMedia can help.
How RadMedia Enables Closed-Loop Resolution
RadMedia exists to finish routine, policy-bound work inside the message and prove it. The service connects to legacy cores and modern APIs, validates identity, encodes policy, and writes outcomes back with idempotent guarantees. That closes the loop, reduces manual reconciliation, and gives you evidence you can hand to audit without drama.
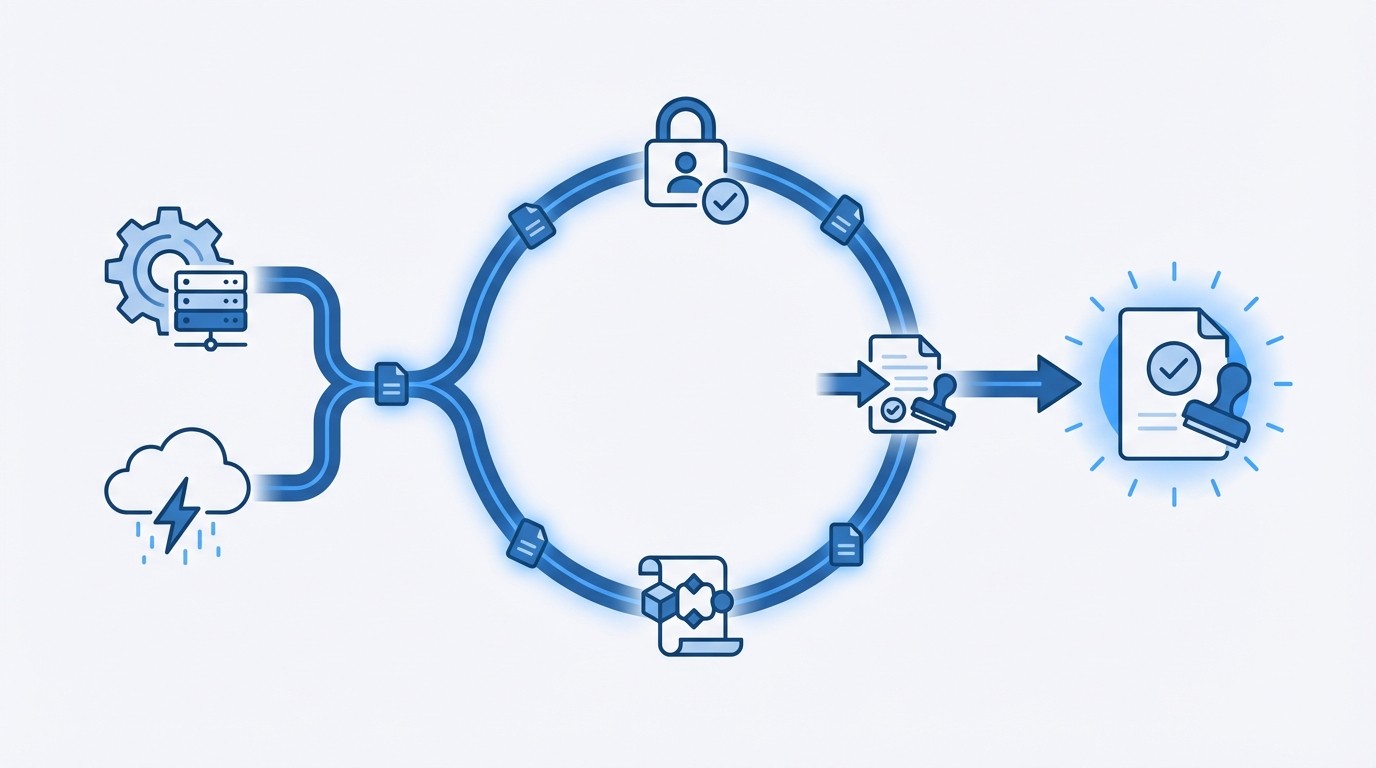
Managed Integration With Writeback Guarantees
RadMedia’s managed back-end integration removes the hardest part of automation. The team owns adapters, authentication, schema mapping, and error handling so triggers flow in and outcomes post back to systems of record without brittle projects. Retries use backoff to protect downstream systems, and idempotent operations prevent duplicate updates under network flaps.
That change shows up in your numbers. Time-to-resolution shrinks because customers act where they already are. Writeback success rises because transactions don’t double or disappear. Manual reconciliation drops, which cuts cost and frees agents for exceptions. For sensitive steps, RadMedia enforces strong security, identity, and audit controls, TLS in transit, encryption at rest, RBAC and optional SSO for operator access, while validating customers with signed deep links, one-time codes, or known-fact checks before exposing actions.
In-Message Self-Service And Policy-Aware Orchestration
RadMedia’s in-message mini-apps let customers update cards, authorize payments, choose compliant plans, confirm details, upload documents, or sign attestations without portal detours. Identity is validated with one-time codes, signed links, or known-fact checks, then only policy-eligible actions appear. The Autopilot engine advances each case with time-based logic and exception routing, so routine work completes without agent touch and edge cases escalate with full context.
Operational visibility is built in. Telemetry tracks deliveries, opens, actions, validations, and writebacks so your team measures completion, time-to-resolution, and deflection, not just sends. Data and logs export cleanly to your analytics or SIEM. Channel orchestration across SMS, email, and WhatsApp respects consent and timing, nudging action at the right moment with links to the embedded app, as documented in the WhatsApp Business Platform.
Fewer manual reconciliations and faster resolution. That is what RadMedia delivers.
Conclusion
You don’t win control by owning every line of code. You win control by proving outcomes, cutting reconciliation, and shrinking incident risk. Treat the decision as risk transfer with evidence attached. Use the readiness checklist, build the risk delta, and test one high-volume workflow.
If you need guaranteed writebacks, identity you can defend, and telemetry you can trust, a managed system of engagement often raises control, not lowers it. Start where the action starts, inside the message, and finish it there. Ready for customer communication workflows on autopilot? Let’s chat.